Hacked terminals capable of causing pacemaker deaths
October 18, 2012
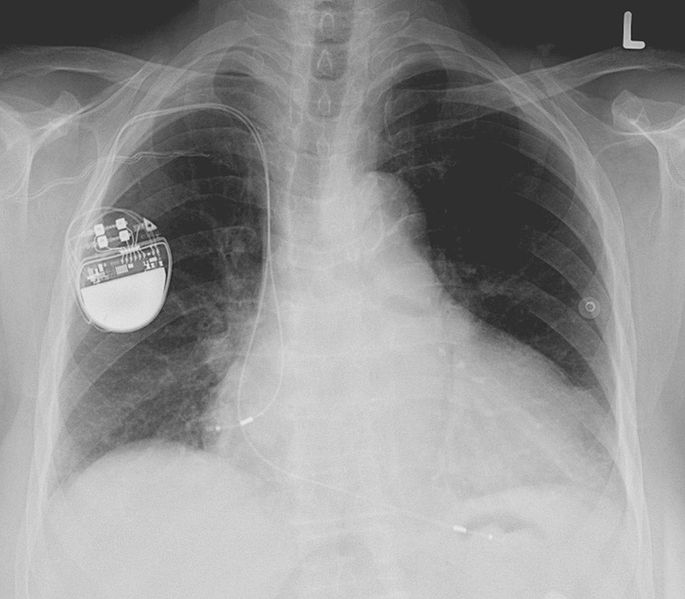
Barnaby Jack, a Research Architect with the TRACE research team at McAfee, has reverse-engineered a pacemaker transmitter to make it possible to deliver deadly electric shocks to pacemakers within 30 feet and rewrite their firmware, SC Magazine reports.
In a speech at the BreakPoint security conference in Melbourne Wednesday, Jack said such attacks were tantamount to “anonymous assassination” and in a realistic but worse-case scenario, “mass murder.”
In a video demonstration, which Jack declined to release publicly because it may reveal the name of the manufacturer, he issued a series of 830 volt shocks to the pacemaker using a laptop.
The particular pacemakers contained a “secret function” that could be used to activate all pacemakers and implantable cardioverter-defibrillators (ICDs) in a 30 foot -plus vicinity.
Each device would return model and serial numbers. “With that information, we have enough information to authenticate with any device in range,” Jack said.
In reverse-engineering the terminals — which communicate with the pacemakers — he discovered no obfuscation efforts and even found usernames and passwords for what appeared to be the manufacturer’s development server.
That data could be used to load rogue firmware which could spread between pacemakers.
“With a max voltage of 830 volts, it’s not hard to see why this is a fairly deadly feature. Not only could you induce cardiac arrest, but you could continually recharge the device and deliver shocks on loop,” he said.
Jack said his goal was not to cause harm, but to help manufacturers secure their devices.